|
https://tcrn.ch/2W2u6F8
Decrypted Telegram bot chatter revealed as new Windows malware https://tcrn.ch/2QZ48is Sometimes it take a small bug in one thing to find something massive elsewhere. During an investigation recent, security firm Forcepoint Labs said it found a new kind of malware that was found taking instructions from a hacker sending commands over the encrypted messaging app Telegram. The researchers described their newly discovered malware, dubbed GoodSender, as a “fairly simple” Windows-based malware that’s about a year old, which uses Telegram as the method to listen and wait for commands. Once the malware infects its target, it creates a new administrator account and enables remote desktop — and waits. As soon as the malware infects, it sends back the username and randomly generated password to the hacker through Telgram. It’s not the first time malware has used a commercial product to communicate with malware. If it’s over the internet, hackers are hiding commands in pictures posted to Twitter or in comments left on celebrity Instagram posts. But using an encrypted messenger makes it far harder to detect. At least, that’s the theory. Forcepoint said in its research out Thursday that it only stumbled on the malware after it found a vulnerability in Telegram’s notoriously bad encryption. End-to-end messages are encrypted using the app’s proprietary MTProto protocol, long slammed by cryptographers for leaking metadata and having flaws, and likened to “being stabbed in the eye with a fork.” Its bots, however, only use traditional TLS — or HTTPS — to communicate. The leaking metadata makes it easy to man-in-the-middle the connection and abuse the bots’ API to read bot sent-and-received messages, but also recover the full messaging history of the target bot, the researchers say. When the researchers found the hacker using a Telegram bot to communicate with the malware, they dug in to learn more. Fortunately, they were able to trace back the bot’s entire message history to the malware because each message had a unique message ID that increased incrementally, allowing the researchers to run a simple script to replay and scrape the bot’s conversation history. 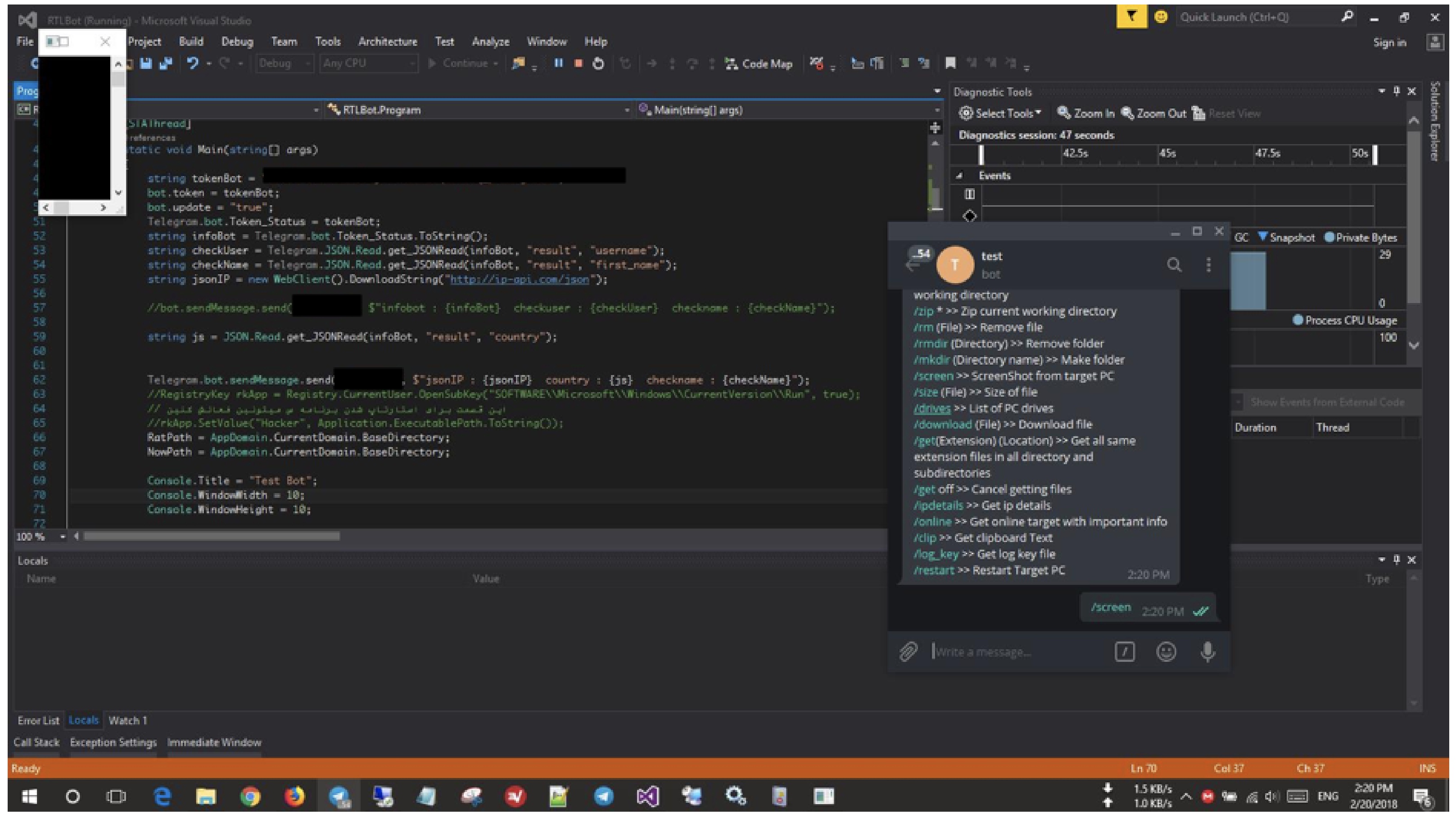
The GoodSender malware is active and sends its first victim information. (Image: Forcepoint) “This meant that we could track [the hacker’s] first steps towards creating and deploying the malware all the way through to current campaigns in the form of communications to and from both victims and test machines,” the researchers said. Your bot uncovered, your malware discovered — what can make it worse for the hacker? The researchers know who they are. Because the hacker didn’t have a clear separation between their development and production workspaces, the researchers say they could track the malware author because they used their own computer and didn’t mask their IP address. The researchers could also see exactly what commands the malware would listen to: take screenshots, remove or download files, get IP address data, copy whatever’s in the clipboard, and even restart the PC. But the researchers don’t have all the answers. How did the malware get onto victim computers in the first place? They suspect they used the so-called EternalBlue exploit, a hacking tool designed to target Windows computers, developed by and stolen from the National Security Agency, to gain access to unpatched computers. And they don’t know how many victims there are, except that there is likely more than 120 victims in the U.S., followed by Vietnam, India, and Australia. Forcepoint informed Telegram of the vulnerability. TechCrunch also reached out to Telegram’s founder and chief executive Pavel Durov for comment, but didn’t hear back. If there’s a lesson to learn? Be careful using bots on Telegram — and certainly don’t use Telegram for your malware. Social Media via Twitter – TechCrunch https://techcrunch.com January 17, 2019 at 07:45AM
0 Comments
Leave a Reply. |
�
Amazing WeightLossCategories
All
Archives
November 2020
|

 RSS Feed
RSS Feed
